Overview
This full-stack platform, built for Kultur Technologies, keeps browser-based messaging fully in-house to satisfy confidentiality, integrity, and real-time workflow requirements. A Go API layer applies AES-256 encryption, PostgreSQL stores all messages plus key metadata, and an HTML/CSS/JS interface delivers a responsive chat experience across desktop and mobile.
Motivation
- Cyber threats and data-leak risks targeting enterprise chat channels continue rising.
- Commercial SaaS tools are costly, closed-source, and often inflexible.
- The goal was to build a company-controlled messaging stack with end-to-end encryption and a customizable web UX.
Project Objectives
- Design secure messaging with AES-256.
- Support real-time text and multimedia sharing.
- Implement strong authentication and access control.
- Model a structured PostgreSQL schema with isolated key storage.
- Provide a responsive front end that optimizes usability.
System Architecture
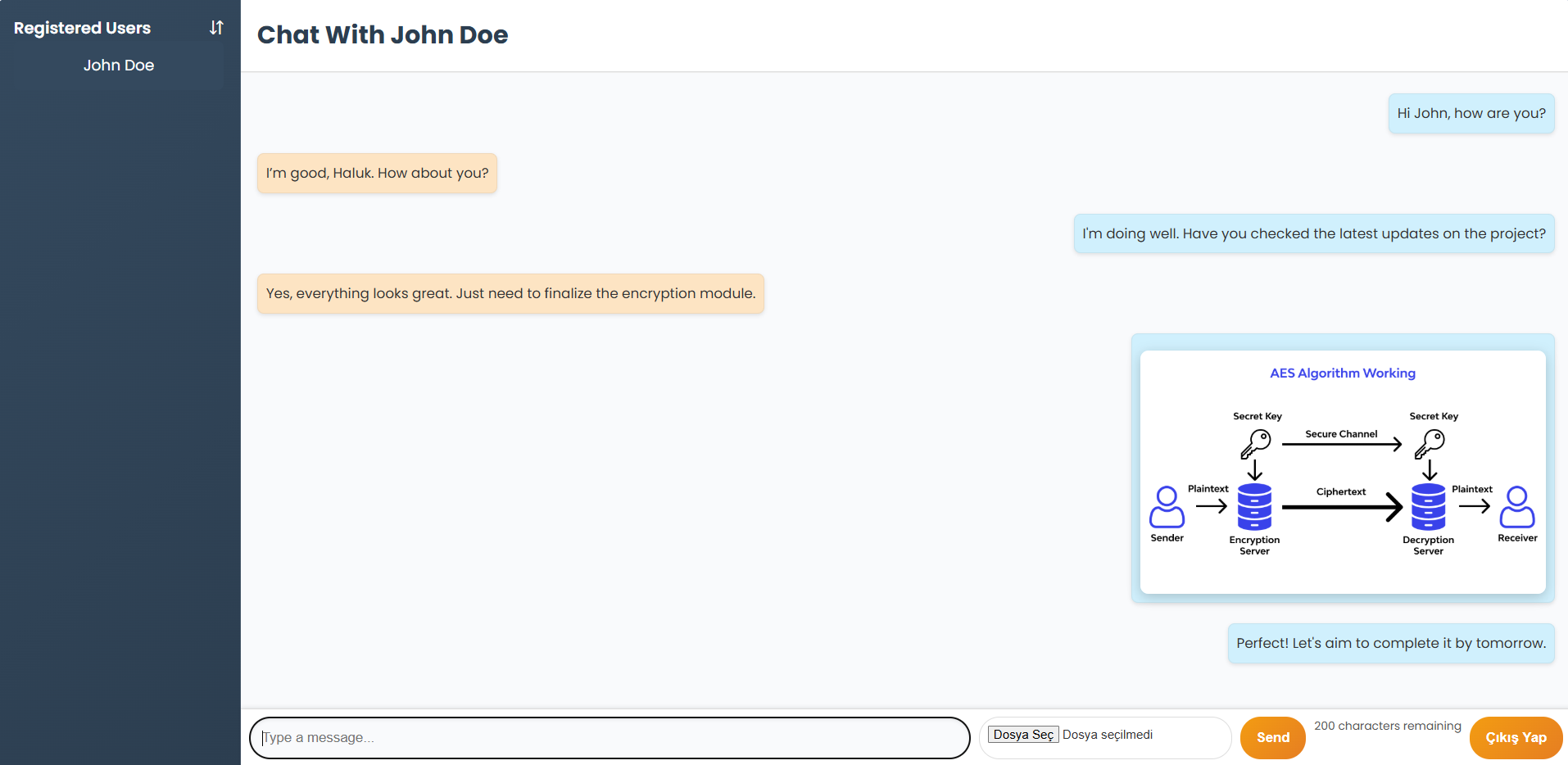
Frontend (HTML5/CSS3/JS)
- Login/registration flows, chat panel, media upload/preview.
- Responsive layouts for mobile and desktop with instant message rendering.
Backend (Go)
- Manages sessions and token validation.
- Routes messages, queues delivery, and leverages Go's concurrency.
- Uses
crypto/aes+crypto/cipherfor AES-256 CBC encryption. - Handles multimedia encoding, API endpoints, and error management.
Database (PostgreSQL)
- Stores user profiles with hashed credentials.
- Persists encrypted messages, timestamps, sender/receiver IDs.
- Keeps 256-bit keys plus IV metadata inside a dedicated MessageKeys table.
- ER model centers on Users, Messages, and MessageKeys to maintain referential integrity.
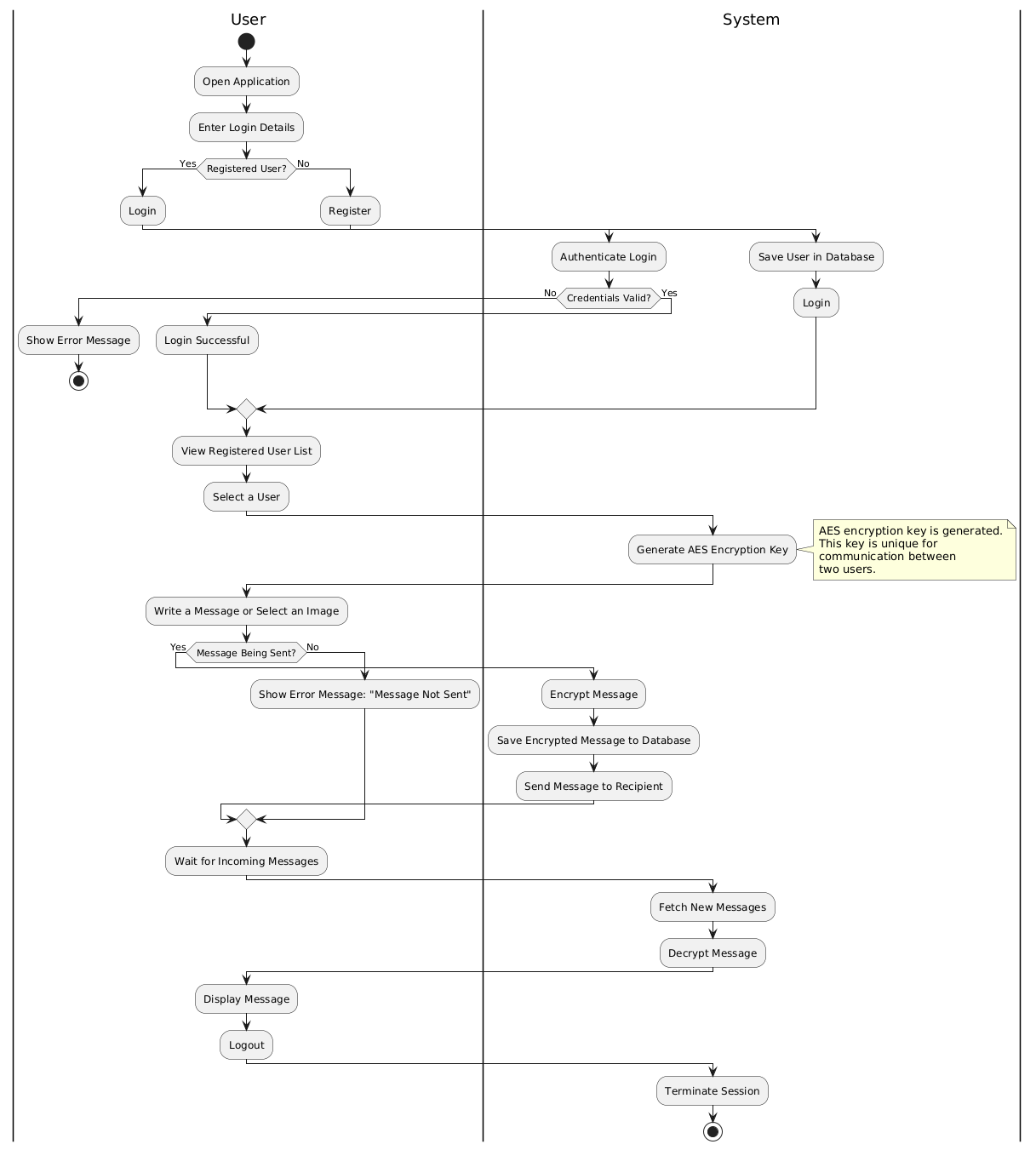
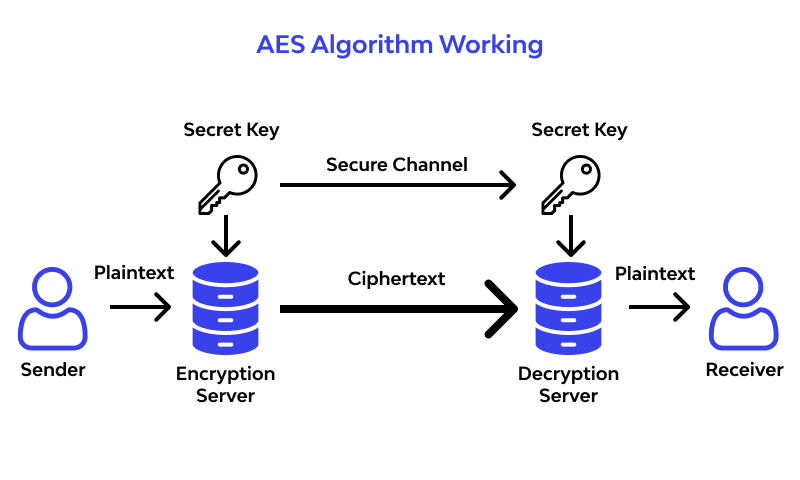
Cryptographic Workflow
- Generate a secure 256-bit key and random IV.
- Encrypt message payload with AES-256 CBC and Base64 encode it.
- Write ciphertext to PostgreSQL while storing keys in a separate table.
- Decrypt only for authorized users; historical ciphers like Playfair or Vigenere were evaluated but rejected for insufficient strength.
Core Functionality
- Authentication: Validates hashed credentials, maintains sessions, and enforces input checks.
- Real-Time Messaging: Enables direct text/multimedia exchange between authenticated users.
- Multimedia Sharing: Encrypts and stores images server-side, decoding them for recipients.
- Key Management: Separates message keys to add another defense layer against unauthorized access.
- Database Integrity: Links every message to both users and key records for full traceability.
Implementation Notes
- Go backend exposes endpoints for message send/receive, authentication, and file uploads.
- Frontend pages (
Auth.html,Chat.html) handle async updates to keep the chat live. - Activity flow: user logs in → backend issues JWT/session → messages are encrypted and stored → authorized clients decrypt on demand.
Testing & Evaluation
- Authentication: Verified valid/invalid login cases and brute-force protections.
- Messaging Stability: Maintained low latency under concurrent message exchanges.
- AES Validation: Confirmed proper error handling for malformed keys/IVs and correctness of encryption/decryption.
- Multimedia: Ensured Base64-encoded images remain intact end to end.
- Cipher Benchmark: Demonstrated AES-256 superiority over classical methods for both security and media compatibility.
Security Strengths
- AES-256 plus isolated key storage keeps database records unreadable.
- Password hashing, form validation, and the modular Go backend minimize attack surface.
- PostgreSQL constraints guarantee consistency and auditability.
Applications
- Internal corporate chat and secure document/image transfer.
- Industries requiring strict confidentiality (finance, legal, consulting).
- Remote teams needing custom, organization-owned collaboration tools.
Conclusion
By combining AES-256 encryption, Go services, PostgreSQL data modeling, and a modern web UI, the system delivers a messaging environment centered on confidentiality, integrity, and operational efficiency. It also lays groundwork for future upgrades such as group chats, automatic key rotation, message expiration, and broader end-to-end encryption features.
Summary
I engineered an AES-256 encrypted, Go-backed, PostgreSQL-persisted browser messaging platform for Kultur Technologies that unifies real-time chat, multimedia sharing, authentication, and key management in one secure architecture.